Advanced IT Security Enhancement
In an age where cyber threats are increasingly sophisticated, protecting your IT infrastructure is essential. Our Advanced IT Security Enhancement services provide a robust defense against potential breaches, ensuring your data and operations remain secure. business resilient against evolving cyber threats.
Threat Intelligence
In the ever-evolving cyber threat landscape, staying ahead of potential risks is crucial. Our advanced threat intelligence solutions provide real-time insights into emerging threats, enabling proactive defense strategies. By leveraging AI and machine learning, we help you anticipate and neutralize threats before they impact your business.
Zero Trust Architecture
Adopting a Zero Trust approach ensures that every access request is thoroughly verified, regardless of its origin. Our Zero Trust solutions enforce strict access controls and continuous authentication, minimizing the risk of unauthorized access and data breaches. This architecture is essential for maintaining a secure and resilient IT environment.
Endpoint Security
Protecting endpoints is vital in safeguarding your network. Our comprehensive endpoint security solutions include advanced antivirus, anti-malware, and intrusion detection systems. By securing all devices connected to your network, we ensure that your data remains protected from potential threats.
Cloud Security
As businesses increasingly rely on cloud services, securing these environments is paramount. Our cloud security solutions provide robust protection for your cloud infrastructure, applications, and data. We implement advanced encryption, access controls, and continuous monitoring to safeguard your cloud assets.
Incident Response
A swift and effective response to security incidents is critical in minimizing damage. Our incident response services offer rapid detection, containment, and remediation of security breaches. With our expert team and advanced tools, we help you recover quickly and strengthen your defenses against future attacks.
Security Awareness Training
Empowering your team with knowledge is a key component of a robust security strategy. Our security awareness training programs educate employees on best practices, potential threats, and how to respond to security incidents. By fostering a culture of security awareness, we reduce the risk of human error and enhance overall organizational security.
Understanding Your Security Landscape
By analyzing your current security framework and an in-depth understanding of your business’s unique risks and challenges, we develop a robust security strategy that safeguards your critical data, systems, and networks from evolving threats. We engage in detailed consultations to gather insight into your business objectives, challenges, and growth plans.
-
Stakeholder Interviews
-
Risk Assessment & Vulnerability Analysis
-
Compliance and Regulatory Review
-
Customized Security Strategy Development
-
Implementation and Monitoring Plan Creation

Building a Resilient Security Framework
Based on the assessment, we design robust security architecture that integrates advanced technologies and best practices. This ensures a scalable and secure environment capable of defending against evolving threats. Our approach includes implementing network security protocols, deploying endpoint protection, and establishing data protection measures to safeguard your business from potential cyber threats.
Network Security Design
Endpoint Protection
Data Protection

Executing the Security Strategy
With the design in place, we move to the implementation phase. This involves setting up the necessary security infrastructure, integrating security solutions, and configuring systems to ensure a seamless transition. Our team ensures minimal disruption to your operations while deploying the necessary infrastructure and configuring systems. This phase includes setting up security hardware and software, integrating new security measures with existing systems, and configuring security policies and user access controls.
Security Infrastructure Setup
Solution Integration
Configuration Management

Ensuring Robust Security Performance
After implementation, we conduct rigorous testing to ensure everything is functioning correctly. This phase includes performance tuning and optimization to ensure your security system operates at peak efficiency. We perform penetration testing, vulnerability assessments, and security audits to identify and address any weaknesses, ensuring your security system operates at its best.
Security Testing
Optimization
Issue Resolution
Empowering Your Team with Security Expertise
To ensure your team can effectively manage and utilize the new security systems, we provide comprehensive training and ongoing support. This includes detailed user guides, hands-on training sessions, and a dedicated support team to assist with any questions or issues that may arise. By empowering your team with the necessary skills and knowledge, we ensure that they are comfortable with the new tools and can use them effectively. Continuous support and feedback collection help us refine the system and ensure it meets your evolving needs.
User Training
Continuous Support
Feedback Loop

Continuous Monitoring and Maintenance
Sustaining Security Excellence Post-implementation, we offer continuous monitoring and maintenance services to ensure your security infrastructure remains robust and effective. This includes regular updates, security patches, and performance monitoring to proactively address any potential security issues. Real-time monitoring helps detect and respond to threats promptly, while regular maintenance keeps your systems secure and up-to-date. Proactive management, including regular reviews and preventative maintenance, helps maintain the long-term success of your security efforts.
Continuous Monitoring
Regular Maintenance
Proactive Management

What clients say about our Services


Success Stories

Saitech Inc. Fortifies Metropolitan Community College’s Cybersecurity with Proofpoint
Saitech Inc. partnered with Metropolitan Community College in Kansas City to strengthen higher education cybersecurity by implementing Proofpoint’s enterprise email security, phishing protection, and advanced threat detection platform under a multi-year BPA.

Saitech Inc. Deployed Getac Rugged Mobility Solution for Mesa County with Lease-to-Own Option
Saitech Inc. partnered with Mesa County to modernize mobile operations for the Sheriff’s Office and patrol fleet, delivering a rugged, future-ready mobility solution designed for demanding law enforcement environments. The engagement combined Getac V120 rugged devices, enhanced in-vehicle connectivity, professional installation services, and a flexible five-year lease-to-own model to ensure durability, reliability, and predictable long-term costs.
Through this end-to-end deployment, Saitech provided more than hardware—delivering a scalable, resilient mobility ecosystem that enhances officer safety, improves operational efficiency, and equips Mesa County with a dependable platform to support mission-critical operations well into the next decade.
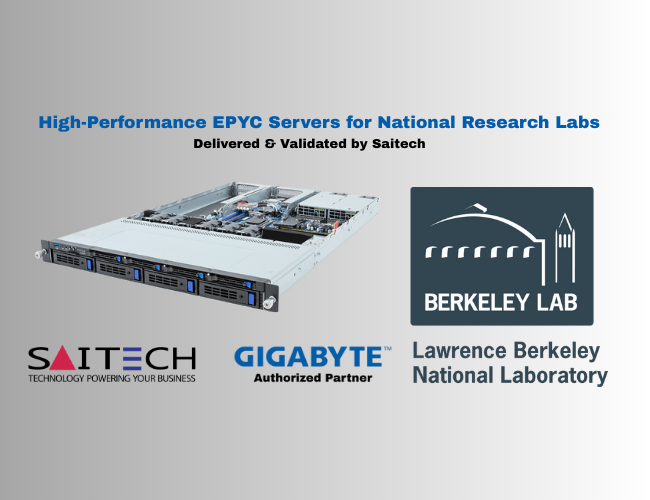
Saitech Delivers High-Performance Gigabyte EPYC Servers for Lawrence Berkeley National Laboratory
Saitech Inc. partnered with the AI cloud service provider to deliver a cutting-edge GPU compute infrastructure designed for modern AI workloads. Leveraging the ASUS ESC8000 platform with AMD EPYC processors and NVIDIA RTX 6000 Blackwell GPUs, Saitech deployed three high-density nodes totaling over $260,000. The solution supports large-scale LLMs, high-concurrency multi-tenant performance, and future GPU scalability, enabling the provider to expand its AI compute offerings, increase GPU rental capacity, and secure a long-term, future-ready foundation for AI innovation.
